Protect your business
with ease
Join over 1,200 companies that already trust us.
VARS continuously analyzes the security industry to identify the best solutions for you.
Secure all your organization’s endpoints, including computers and servers, to block access by cybercriminals.
Phishing, compromised accounts, ransomware and identity theft are just some of the threats that come from emails.
Hackers collect sensitive information on the dark web to prepare cyberattacks against your organization. We can help.
Cybersecurity awareness and training are some of the key components to create a mature security culture within your organization.
OUR CERTIFIED CREDIBILITY









In Case of Cyberattacks
In a world increasingly focused on automated cybersecurity, maintaining human contact within the concept of SOC (Security Operations Center) is essential. Beyond technologies and monitoring tools, with VARS, the human factor remains a central pillar for analyzing alerts, interpreting security data, and making informed decisions.
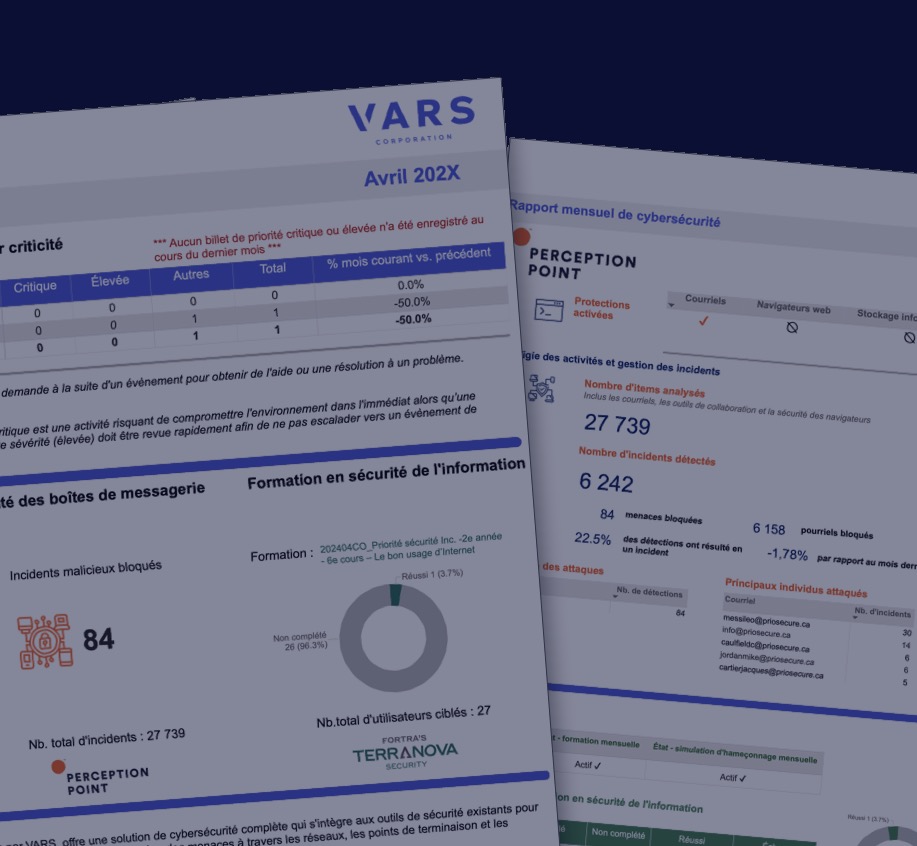
VARS’s complete monthly security report
Every month, you can examine a customized security overview of your organization, to get a clear picture of the attacks VARS intercepted, as well as any security issues identified. In short, you’ll benefit from an essential tool for informed decision-making.
THE BEST PROTECTION
These essentials are at the heart of our integrated and fully customizable solution. Save months of effort, reduce your risks, and secure your business today.
The integrated solution provided by VARS is fully customizable and, therefore, we bring you the best cybersecurity solutions on the market, then make recommendations on which ones are best suited to protect your organization’s digital environments. VARS will then handle the deployment of these solutions to maximize your cybersecurity.
As a cybersecurity solutions reseller, we are in the best uniquely position to assess which solutions are best suited to the changing needs of local businesses. We are not tied to any one solution, but rather partner with several, which allows us to constantly challenge the status quo and further develop our range of integrated solutions.
Absolutely. You will receive a monthly automated performance report giving you a comprehensive overview of the analyses carried out, blocked attacks, etc. In short, this unique report will give you an overview of the performance of our solutions designed to protect your digital environments.
These are a few of the benefits a solution managed by VARS offers
Yes. The strong relationship VARS has established with global cybersecurity solution providers allows us to offer a wide range of cybersecurity services, tailored to both SMEs and large companies. In short, we strive to democratize the best solutions on the market by making them accessible to businesses of all sizes.
As a cybersecurity solution provider, our client base allows us to negotiate the most attractive pricing agreements with the world’s leading suppliers. In addition, VARS is not tied to any particular solution or supplier, so we ensure that we are constantly developing our service offering to maximize your organization’s security in a world where cyberthreats are evolving on a daily basis.